The role of identity verification in the digital age cannot be underestimated. Explore the importance of verifying identities online and how it safeguards against fraudulent activities in this comprehensive guide.
One of the most strategic ways to access a system is using unauthorized details or fraudulently obtaining authorized details to gain access to the system. This approach is much easier for attackers since they can hardly be noticed, and neither do they have to spend on attack resources.
Notably, identity theft and related attacks can originate from internal sources, i.e., employees using the details of others to access the system fraudulently. However, most cases are usually from external sources with stolen identities or help from the inside, knowingly or unknowingly.
Due to these concerns, companies need to enforce strict identity verification to prevent attacks by verifying system logs to ensure they are all recognized by the system or an administrator. Identity verification is crucial, and the roles are vast, including securing customer data, and company trademarks, boosting customer trust, and enforcing backup security measures.
Let’s explore each of these benefits in detail.
Role of Identity Verification in A Digital Age:

1. Fraud Prevention Measures
One of the main concerns for companies is fraudulent access to private databases, especially those containing confidential data, which can be used as ransom leverage or competitive advantage. The threat of fraudulent access is internal and external; as various parties can successfully create fake accounts and use false or stolen details to gain access.
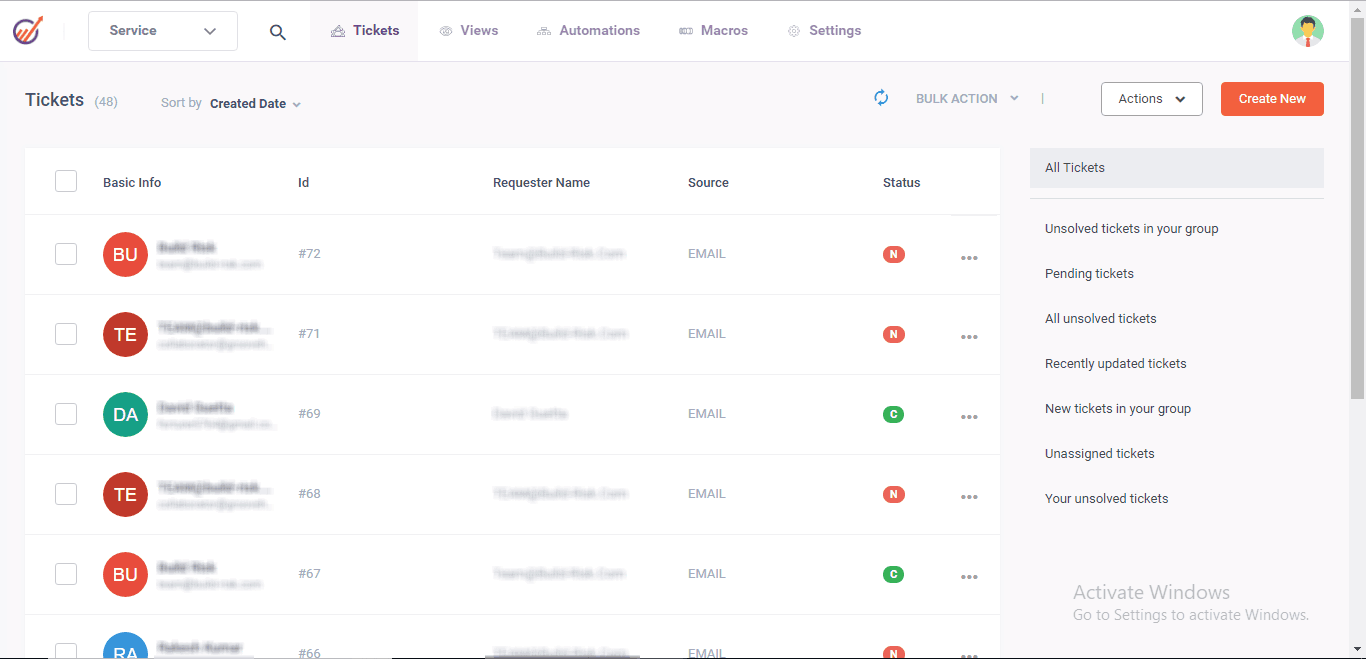
In such cases, Identity verification is necessary to ensure only authorized and recognized individuals and devices can access business systems.
By following various authentication guidelines and steps; companies can secure all the systems and activate instant alerts to notify in case of any fraud. For companies dealing with details such as documentation and vast data; identify verification can confirm details such as information and data sources to ensure quality, reliability, and data is not compromised or from fraudulent sources.
Such measures can be implemented for various communication channels to ensure employees are protected from fraudulent emails to attack the systems.
By enforcing different identity verification measures, companies can ensure employees only access certain levels of data where they have access clearances. This involves enforcing access level verification guidelines that verify employee and device details before granting access to private and confidential data.

2. Protecting Online Identities
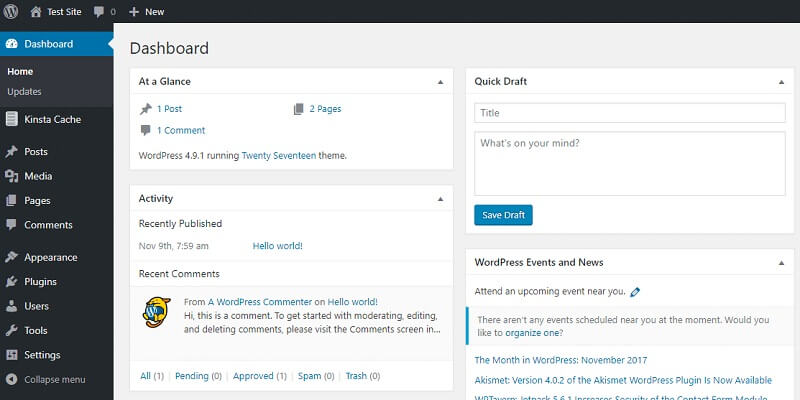
Nearly all the activities today are conducted on online platforms that is, e-commerce, communication, customer engagement, and other activities. Due to its vast capabilities, it is also a significant target by hackers targeting private communication, details, and other data sharing amongst individuals and companies. For communication platforms such as company internal communication and customer engagement channels; there is a need for identity verification to protect private data and communication.
Through verification, only the cleared parties and stakeholders can be part of these communications and access data shared through private communication platforms and servers. This involves establishing systems and individual identity verifications using biometrics, passwords, and certificate-based security authentication measures to ensure only the accepted team can be part of the platform.
Another need for these identification strategies is ideal whenever the organization outsources systems and software. For instance, when the company outsources a cloud platform; these identification verification security measures are essential to ensure that third parties cannot tap into the private platform. Therefore, all the details remain private, including the details of those involved in the communication and using the system at any time.
3. Improved Relationship with Customers
Identity verification is ideal for customer management services since it ensures communication security and consumer details are kept a secret. Through identity verification, company data can hardly leak to the wrong people and attackers; therefore, customers are assured of their data security.
A positive reputation is ideal for boosting customer loyalty and attracting more customers to the business to ensure it maintains its market share. Additionally, the communication between the customers and company employees is secure and can hardly be accessed by unauthorized parties; thereby maintaining confidentiality.
Companies are also dealing with fraud; especially from individuals who pretend to be company employees to scam the company’s customers. Only the legal and authorized parties can contact the customers, and all communications are kept in the company database. In case of any complaints, the company can refer to the information; use it for investigations and ensure customers are treated appropriately.
Through identity verification; all the customer information and details are secure; thereby boosting long-term relationships with them. It is the first and most significant step to building a lasting relationship with customers.

4. Multiple Protection Strategies
Customers, organizations, and employees are vulnerable to attacks from various sources, such as stolen details and compromised security; therefore, you should enforce backup security measures. For instance, when a customer’s bank cards are stolen or accounts taken over by attackers; ensure there are multiple identification protocols to impede access by unknown parties. This will protect the customers from losing their resources; further boosting their trust in the organization.
For employees, you can implement multifactor identity verification to ensure they use a combination of security measures, i.e., tokens, biometrics, and passwords, to access the devices. In case one is compromised, i.e., a stolen phone or password; the other security measures protect the company data.
At company levels, multiple identity verification strategies such as AI-driven identity verification, biometrics, and certificate-based authentication are ideal for securing confidential data and detecting potential fraud, fake accounts, or intended attacks.

Conclusion: Role of Identity Verification
Verification in the digital age is more than granting access to the company system; there are more benefits the company can enjoy beyond identity verification. It is ideal for boosting company reputation; customer relationships, securing communication channels, and preventing fraudulent system access.
Enforcing strict identity verification is also ideal for protecting online identities on various platforms; such as social media platforms and e-commerce websites.