PKI plays a crucial role in ensuring secure communication and authentication in the digital world. Discover the significance of Public Key Infrastructure and how it works in this informative guide.
Our lives are now digitally connected and heavily reliant on the internet. Therefore, being aware of the importance of PKI is like possessing the key to a knowledge vault. Why bother deciphering this mysterious-sounding acronym, you might be asking.
The answer is straightforward: PKI is an invisible watchdog to ensure your online transactions are secure. PKI operates in the background while you exchange emails, shop online, or browse the web. It assures you communicate with dependable organizations while protecting your data from snoopers.
So, take a figurative magnifying glass as we set out on a quest to discover PKI’s mysteries. We’ll explain the nuances, consider how they apply in real life, and illuminate how they affect your digital life. You’ll have a greater understanding of PKI’s role in maintaining the functionality and security of our online environment by the end of this investigation.
What is PKI?
PKI is an acronym for Public Key Infrastructure. We want you to consider it as the champion of safe digital communication and data security. It’s a technical spin on a lock and key system for your online surroundings.
You have two key pairs—one private and one public. The public key, accessible to everyone, is the friendly key. Anyone can put a message in it, much like a mailbox, but only the owner of the private key can open it and read what is within.
What about that secret code? It is just as private as your front door key. Your particular access code is that. Only your private key can decrypt a communication that someone sends to you using your public key.
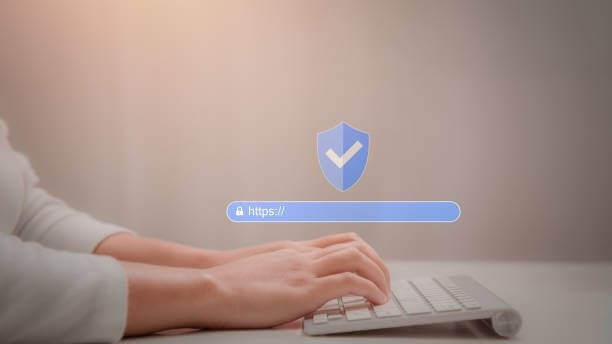
PKI is amazing because it handles your web browser, displaying the comforting “https” for safe internet browsing. Large corporations, such as Microsoft, rely on it for solid security. Microsoft PKI is a subset of PKI technology created and made available by Microsoft for its operating systems and software products.
PKI also aids in online identity verification by utilizing digital certificates issued by reputable Certificate Authorities. Further, the secret underlying email encryption keeps your messages confidential.
The Significance Of Public Key Infrastructure
1. The Trusty Certificate Authority (CA)
Let’s talk about trust now. How do you know the public key you share belongs to you and isn’t a dubious forgery? Certificate Authorities (CAs) come into play in this situation.
The trustworthy companies that offer digital certificates are known as CAs. Digital ID cards and these certificates also serve comparable purposes. Your browser verifies the certificate with a CA when you access a secure website to ensure its validity. PKI has your back, so stop falling for phony websites.

2. Ensuring Privacy with Encryption
In the digital age, privacy is crucial, and PKI is your hidden protector. PKI uses its superpower of encryption whenever you send a message, make an online purchase, or do anything involving sensitive data. Using the recipient’s public key scrambles your data into an unintelligible jumble.
The information cannot be decoded or accessed by anybody other than the recipient holding the correct private key. It’s comparable to transmitting a coded message only your pal can read.
3. Protecting Data Integrity
Let’s assume you’re sending a contract or a love letter, both of which demand security via the Internet. You want to be sure that nothing has been tampered with while the document travels. Again, PKI comes to the rescue!
It makes use of digital signatures to guarantee the integrity of your document. Anyone with access to your public key can verify if a document you digitally sign with your private key is still in its original format. It’s like using your special wax stamp to seal an envelope; you’ll immediately notice a problem if the seal is no longer there.
4. Versatility
PKI is used for more than just safeguarding websites and email. It’s a digital Swiss military knife employed in various industries, from healthcare to banking. It preserves the privacy of patient statistics in healthcare, so your clinical history remains personal.
Also, it’s the backbone of net banking in finance, ensuring your transactions are rock-stable and safe. The diversity of PKI is remarkable, and it attests to its significance in our virtual life.

Challenges and Staying Ahead
Let’s not act as though PKI has it simple. It might be challenging to manage all those certificates, ensure they are revoked when required, and keep a solid infrastructure. Not to add that the bad guys are continuously coming up with new ruses in the internet realm, which is something like a Wild West movie.
One of the newest kids on the block, quantum computing, has the potential to upend things. Quantum computers can break present encryption protocols more quickly than you can say “PKI.” Don’t worry; the PKI’s brilliant creators are already developing post-quantum cryptography to keep up.
Closing Thoughts: Significance Of Public Key Infrastructure
PKI is the unsung hero that keeps us safe in an age where cyber threats are everywhere online. It explains why you can securely browse the web, sign documents, and divulge your private information online.
Take a moment to appreciate PKI’s invisible hand at work protecting you the next time you send a private message or make an online purchase. The ultimate superhero of the digital age, it protects your online activities and leaves you worry-free even if it doesn’t wear a cape.